Magento sites Hacking Rescue Team

Is Your Magento Site Hacked?
Hire Magento Developer from AALOGICS (Karachi, Pakistan)
We all know that Magento is a very reliable and much protected platform. However, it is likely that if any part of the server or system is unprotected then this could hack the Magento site. Therefore, Hire Magento Developer from AALOGICS (Karachi, Pakistan) a team leaded by certified Magento developer and in-house team of 12 expert developers that will inspect and eliminate the infection on your Magento website.
Previously, many clients contacted us and Hire Magento Developer from AALOGICS (Karachi, Pakistan) for their infected Magento sites.
3 Reasons Why Magento Sites got Hacked:
1. Draw attention to oneself / Defacing
In this case, the hackers are simply attempting to strive the Magento business site as to draw attention to his friends that he is skilled and can control over a site. More popular your site, the more showoff rights he gets.
- What the hacker do ?
Generally the hacker damages the landing page or erased the records. - How this hacking take place ?
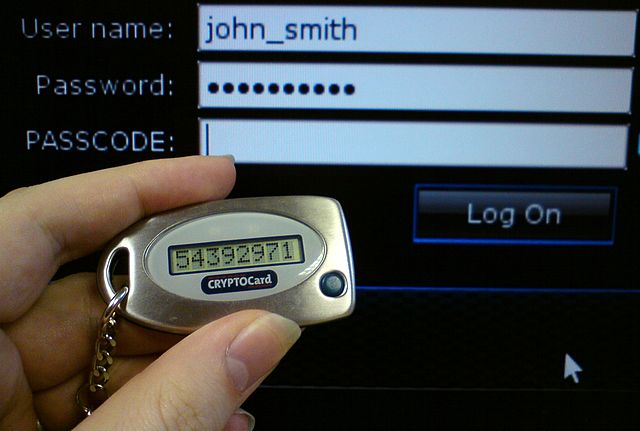
This hacking happens due to powerless passwords in an Admin range, FTP, or different means. However, the database is frequently not influenced. - In these types of hacking, the messages are unpleasant and mocking. It's often not in any case individual or directed toward you or your association.
- To prevent this, AAlogics Magento Support team suggest their clients to limit their sites from a couple of nations where they are unrealistic to have clients.
2. Damage the server / Phishing site
For this situation, the programmer doesn't generally do anything to your Magento site, however makes a file some place on your site. They may have an email that is conveyed to individuals requesting that they sign into their Facebook, PayPal or Banking Website. Also, when they do, it takes their username and passwords, and after that sends this data out to an alternate server.
On the other hand, they are attempting to utilize a portion of your site to deliver spam email messages. This is generally brought on by having files on your site set to 777 authorizations - implying that anybody can openly compose records to a server.
In case you're hit by this kind of infection, you'll likely be searched out quickly. Google looks over locales and on the off chance that they see any kind of malware, they will close access to your site from indexed lists and in case you're utilizing the Chrome browser, that, too.
PayPal is additionally truly proactive. There are situations where a site is corrupted and they are calling, messaging and attempting to get a site stable within minutes or hours of infection.
Just to Fix this :
- Our Magento Hacking Support team will remove the infected files immediately.
- As Google closed access to indexed lists of your site - Our Magento Hacking Support will submitted a response to Google of site recovery
- Lastly, AAlogics Magento Hacking Support team will put a strong lock at your site for hackers.
3. Taking Valuable Information Like Credit Card Information
What do almost all Magento sites have in like manner? They take online installments and store client data. Presently Magento is generally extremely secure, and a PCI compliant payment gateway, (for example, PayPal Pro or Authorize.net) never for the most part stores Mastercard data on a site. Even so, the previous couple of weeks, we've seen various distinctive adventures on Magento destinations where a couple documents have been adjusted to save client data and charge card information, including CVV2 codes, expiration dates and more and then allow someone to download the file for later use.
We've witnessed this through:
- Catalogs that have open access (i.e. CHMOD 777, for example, a picture upload catalog.
- Other outsider frameworks that are on a site, but not part of a Magento site. For instance, they may have a WordPress blog on the website that is unsecured, and the hacker got along these lines and after that infect the Magento website from an alternate directory.
- Fake extensions that are placed into the Magento Module directory. If the right type of a file is placed in the downloads directory on a site, Magento will often try to run this and to install the module. We've seen fake company names associated with the extensions, including some of the more demanding Magento modules out there.
4. Hacking for Ransom (Kidnapping your Magento Store)
This kind of hacking block the site owner from using their own site until the amount of money is paid to the hacker. In this, the hacker uses a malicious software and encrypt the website's code. The ransomware typically request payment in a hard, such as bitcoin.
Featured Articles

Case Study | Multi-Platform eCommerce API Integration for Lingotuner SAAS : Magento, WooCommerce & Shopify Extension Development
Read More
East West Souk eCommerce Operations Transformed by AAlogics Using Odoo
Read More
How Spectra Solar Optimized Its Lead Generation System With Odoo 17 CRM and Custom API Integration
Read More
Overcoming Odoo Manufacturing Challenges: Why ERP Setups Fail on the Factory Floor
Read More